Management Platform
i4Twins Management platform Provides seamlessly User Management, Device Management, Data Management, Application Management, authentication and authorization, Access level Management with ease, and instantly web-deploy clients to anyone, anywhere.
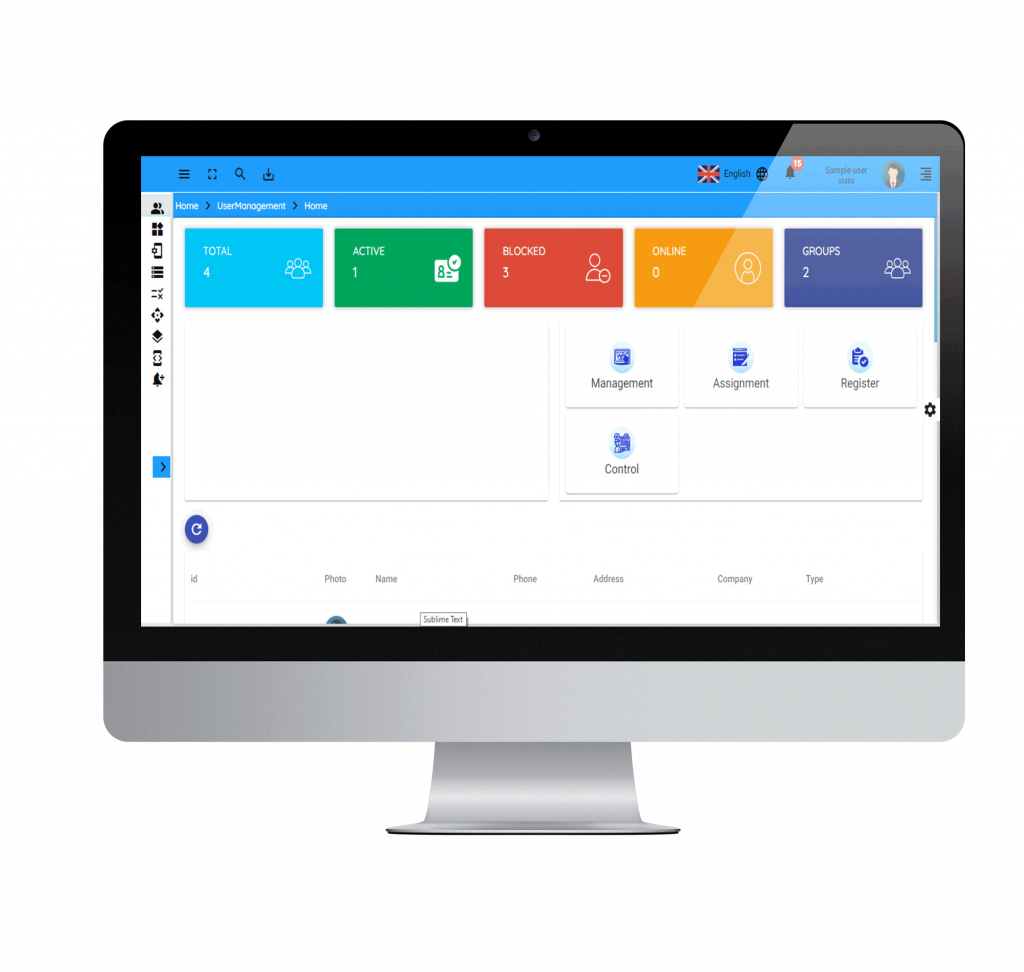
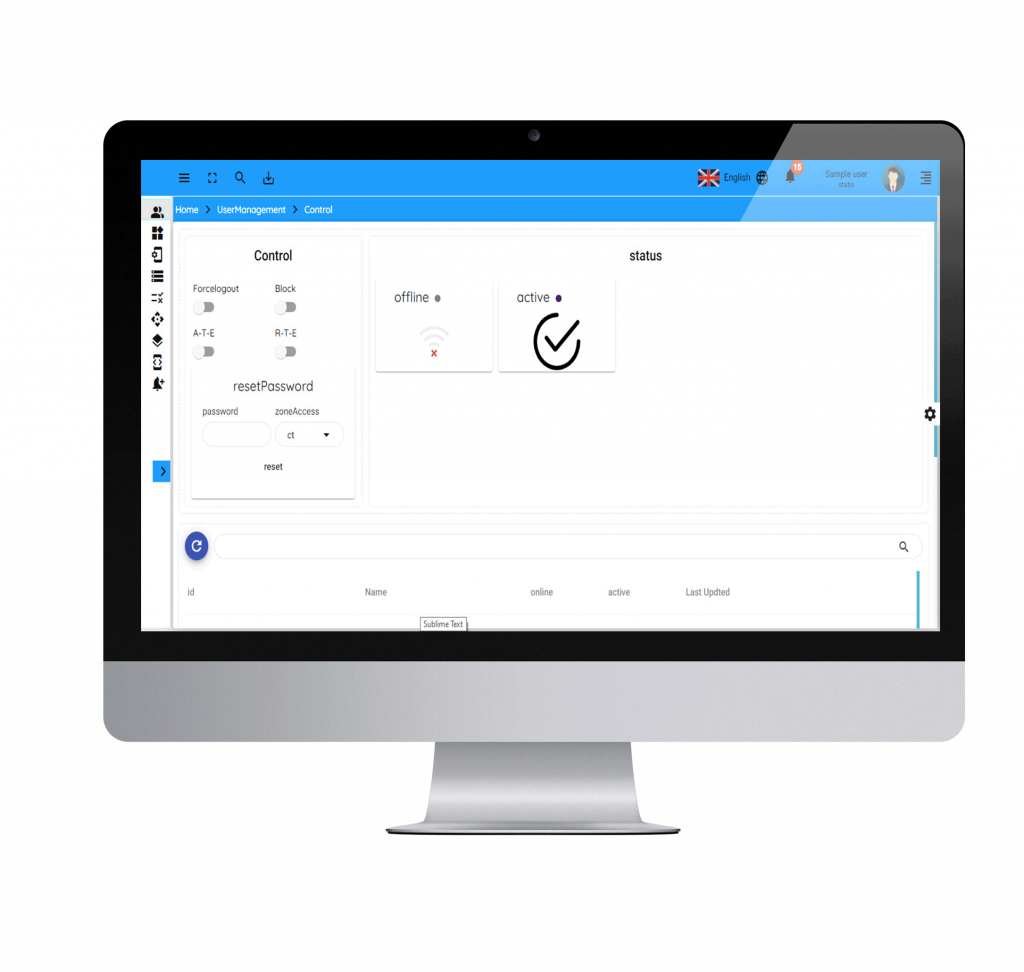
User Management
i4Twins user management implementation involves a wide range of functionality such as adding/deleting users, controlling user activity through permissions, managing user roles, defining authentication policies, resetting user passwords, etc.
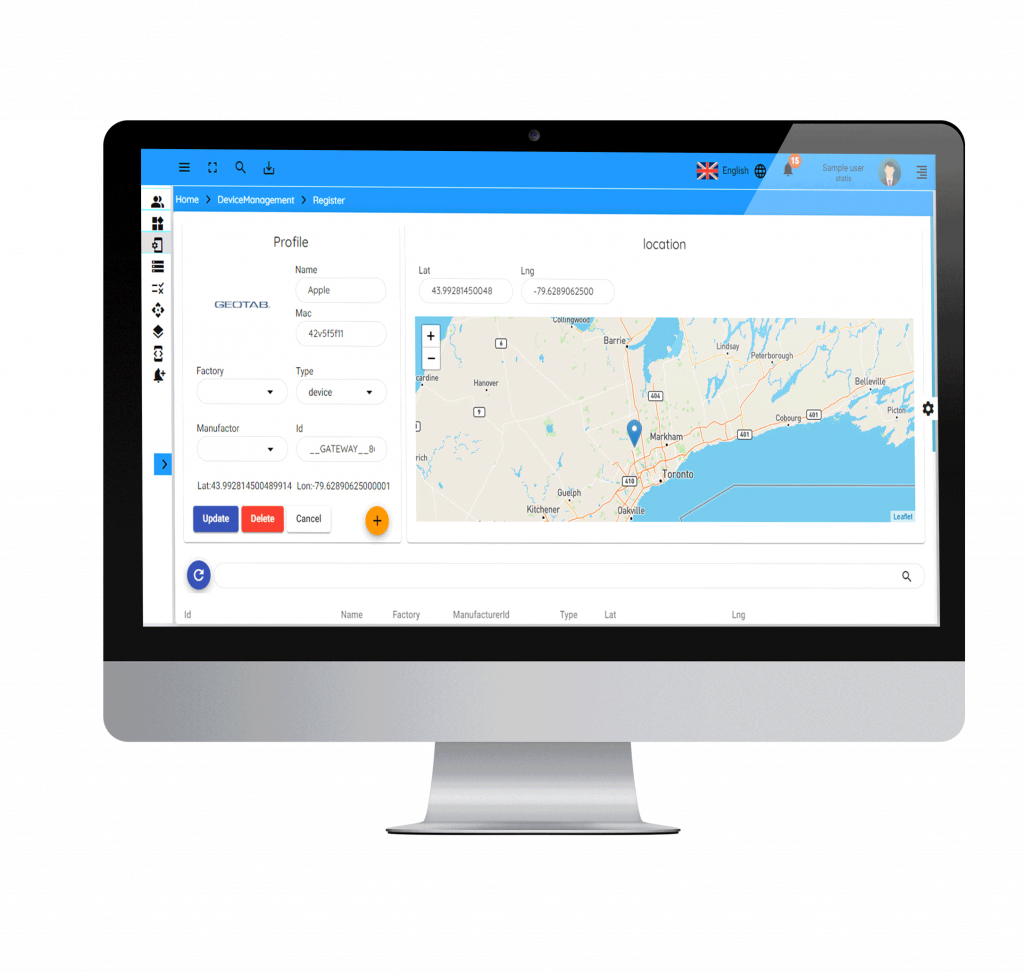
Device Management
i4Twins device management can establish a connection to a device, and obtain information about its state. We help solution developers shorten development and testing time to bring products to the market in a timely fashion. i4Twins device management offers simplified provisioning, centralized management and real-time insights into all current devices and integrations to help companies stay on top of their deployment.

Data Management
i4Twins data management solution can handle all IoT data demands
- Versatile connectivity: wide range of protocols (MQTT, OPC, AMQP, and so on).
- Edge processing: to be able to filter out erroneous records coming from the IoT systems before ingesting it into the data lake.
- Big data processing and machine learning: Operationalize ML models such as anomaly detection in real time.
- Real-time monitoring and alerting: provide real-time monitoring with flow visualizations to show the status of the process at any time with respect to performance and throughput
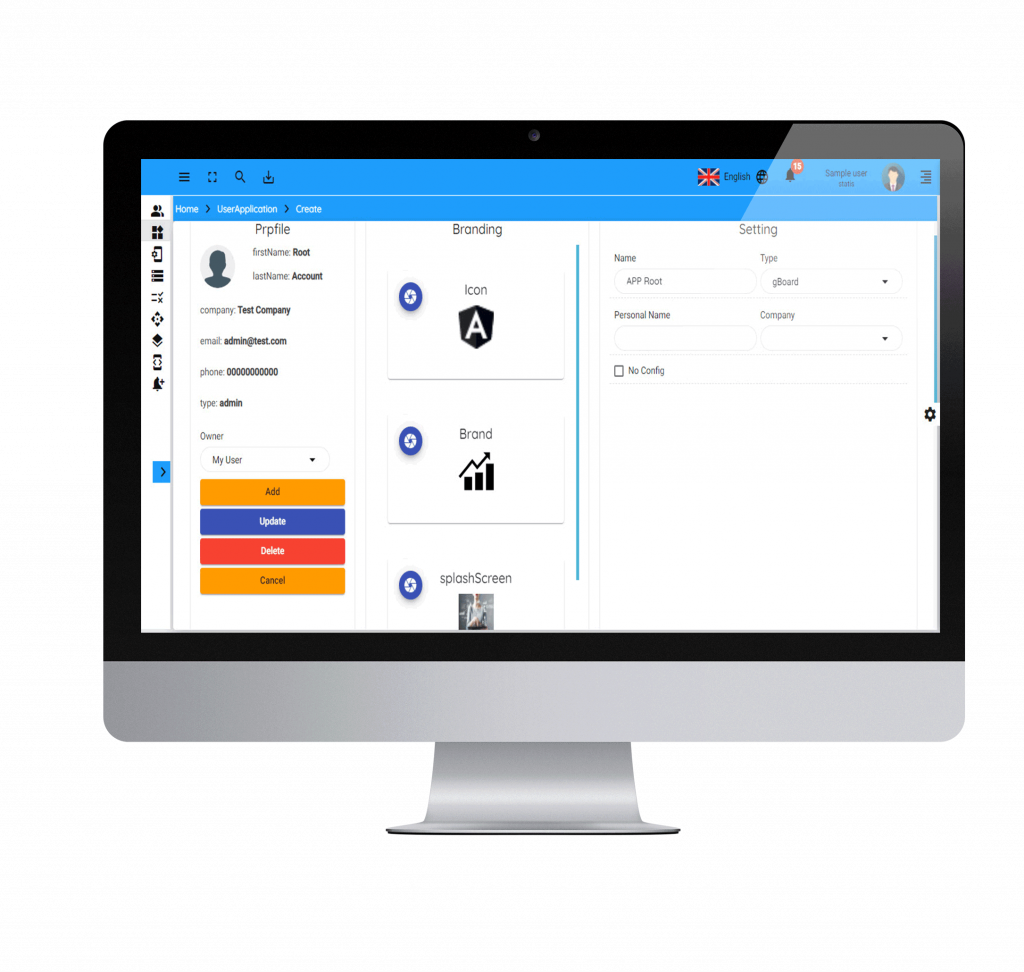
Application Management
i4Twins application management is the glue that allows you to make operational decisions and better manage your business. As organizations plan their IoT projects, there are often many aspects that are not considered in advance, which creates challenges. i4Twins application management is not just about management, but the ability to create business solutions.
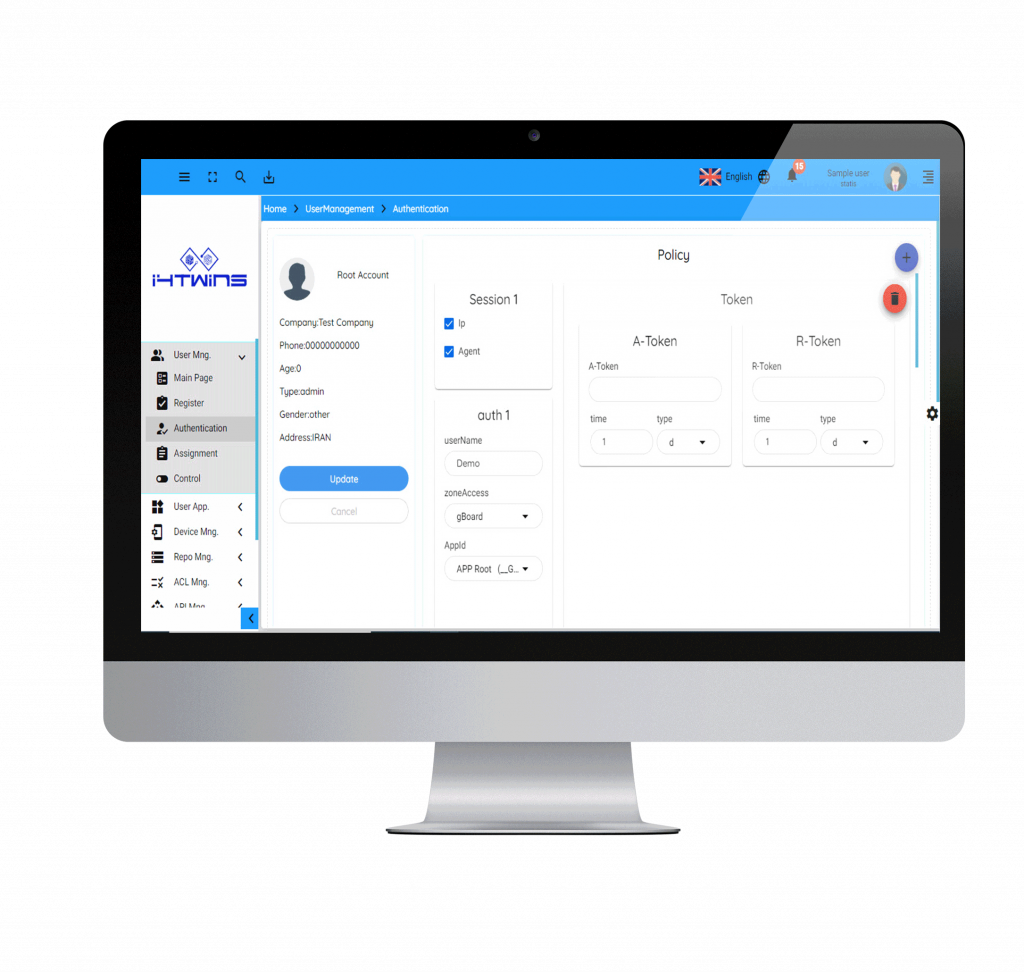
Authentication and Authorization
Authentication and authorization are essential parts of basic security processes and are sorely needed in the platforms. i4Twins provides a mechanism to bind a specific device and users to certain permissions. our authorization microservice is the tool used to validate the identity of each endpoint in the systems.
Access Level Management
i4Twins access control is a set of permissions for both device and user access. Roles are created for the various job functions in an organization or a use scenario and users are assigned roles based on their responsibilities and qualifications. Roles can be granted new permissions as new applications and systems are incorporated, and permissions can be revoked from roles as needed. Permissions are assigned through the user interaction module, translated into access control policies at the backend module, and enforced by the manager module.
About Us
i4Twins is a game-changing solution to provide the bridge the gap between the PHYSICAL and DIGITAL WORLD.
Contact
- info@i4Twins.com
- Highway Innovation Factory, Tehran, IRAN
- 2 Simcoe St,South Suite 3000, Oshawa, Canada